A user’s role defines the actions the user is allowed to perform on a given resource. The role determine the user’s authorized activities on the given resource, ensuring that a user has access only to the functions necessary to complete applicable operations. This allows domain control over specific resources, or system-wide control if your right has no restrictions.
■
| |
■
|
The scope of a role determines what resources a particular user can view. The following scopes are available for NSX users.
The Enterprise Administrator and NSX Administrator roles can only be assigned to vCenter users, and their access scope is global (no restrictions).
How to Assign Permissions to vCenter Local Users in NSX
1. Click on Networking and Security in vSphere Web Client
2. Click on NSX Managers
3. Click on Users under Manage tab and then click on add user option
4. Specify the name of the User to Whom you want to assign the permission
Note :- This user must have vCenter Administrator Role as well
5. Select the appropriate role and then click on finish
How to Assign NSX Roles to SSO
Whenever we want to assign role on NSX, we can assign role to SSO User or Group. When Lookup service is not configured then the group based role assignment would not work i.e the user from that group would not be able to login to NSX.The reason is we cannot fetch any group information from the SSO server. The group based authentication provider is only available when Lookup service is configured. User login where the user is explicitly assigned role on NSX will not be affected. This means that the customer has to individually assign roles to the users and would not be able to take advantage of SSO groups.
For NSX, vCenter SSO server is one of the identity provider for authentication. For authentication on NSX, prerequisite is that the user / group has to be assigned role on NSX.
Note: NTP/DNS must configure on the NSX Manager for lookup service to work.
Note: The domain account must have AD read permission for all objects in the domain tree. The event log reader account must have read permissions for security event logs
Note: Configure Domain is not needed for RBAC, only if we want to use identity firewall rules base of user or group.
1. Configure Lookup Service in NSX Manager 2. Configure Domain Information in NSX Manager From vSphere Web Client
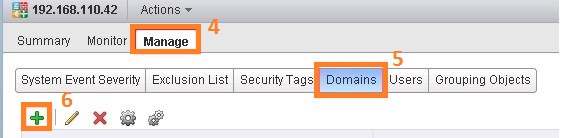
3. Configure Domain Name
3. Configure Domain Controller Information
4. This configuration allow the NSX Manager read Active Directory “Security Event Log” this logs contain Active Directory users logon/logoff from to domain
NSX used this information to improve user identity firewall rules.
5. Review the Details and Click on Finish
6. Map AD groups to NSX Manager Roles
7. Select Specify vCenter Group
8. Type the Group Name
9. Select the appropriate Role
10. Select the access scope that is appropriate for the users
Source:-
http://www.routetocloud.com/2014/10/nsx-role-based-access-control/


















No comments:
Post a Comment